I host my own email, DNS, website, and many other services, so I figure I should probably host my own mastodon instance as well. Plus as @aral always says, it's good for the Fediverse to have more smaller instances.
So I'm going to attempt the Mastodon server migration now, which means if you follow me, it *should* automatically move you. If not, you can follow me @kyle.
Ok, probably my last push. If you considered retweeting about my book, maybe this one makes sense. B&N has a GREAT deal on pre-orders, including mine. :) https://www.barnesandnoble.com/w/my-big-round-world-shawn-powers/1143387025 (Or signed copies are available, details here: https://snar.co/book1)
@chrichri @biktorgj @martijnbraam In case you didn't saw it, we corrected the article to state that the responsible software is not executed as firmware but in the operating system. Requests to android.clients.google.com also originate from microG. https://www.nitrokey.com/news/2023/smartphones-popular-qualcomm-chip-secretly-share-private-information-us-chip-maker
"Microsoft Edge sends a request to bingapis .com with the full URL of nearly every page you navigate to"
Microsoft secretly tracks people across myriads of websites/apps via pixel. Now it was caught tracking them directly in the browser, by default. Wild.
https://www.theverge.com/2023/4/25/23697532/microsoft-edge-browser-url-leak-bing-privacy
@leetaur Thank you!
@giglioli For the super-near-term I'm going to finish writing a new book I started after my Best of Hack and / book, about how to write a tech book (it's so meta, I know).
Beyond that, I don't know. Open to suggestions and opportunities.
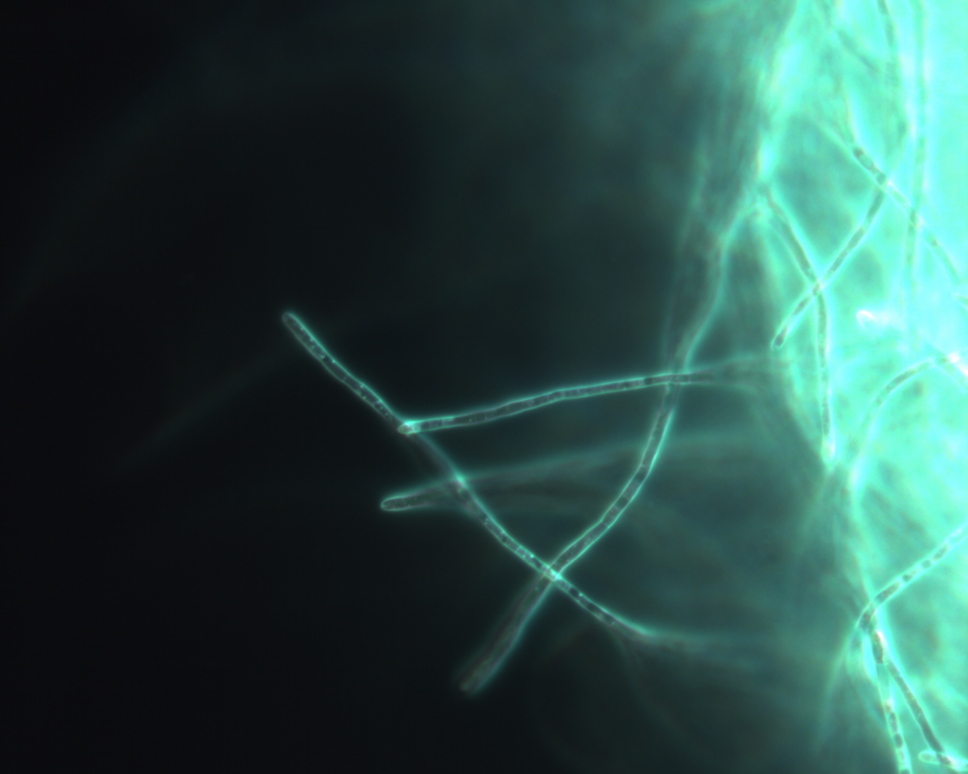
@avanc Yes, I document my whole project here: https://kylerank.in/tempus_nectit/
Today is my last day at Purism after being there for over five years. I'm marking the event on my Tempus Nectit knitting machine clock with a white stripe.
Remember when I drew a comic every day? Well, there were a lot of days of that. And today, a bunch of those @mybigroundworld comics became... A BOOK! (a discounted pre-order book even...)
Details are in my free newsletter: https://nerdlings.substack.com/p/my-little-square-book #book #comic
@hehemrin @katherined Thank you!
I love how on-brand this is for @kyle . It turns out you can DIY your tech book AND do it all in VIM. https://reality2.social/@reality2cast/110261196782461424 #winning #opensource #publishing
Tune in to our new episode! @katherined and @dsearls talk to prolific tech author, @kyle, about how he recently self-published his latest book, and how that differs from his many experiences with traditional publishers.
Visit the following link for full episode - https://www.reality2cast.com/144
@martijnbraam I appreciate your posting a follow-up and analysis of this post. I skimmed (and even boosted) that article this morning because I was curious about the claims and what would come of it after more eyeballs were on it.
NitroKey disappoints me...
@shawnp0wers So exciting!
Smartphones With Popular Qualcomm Chip Secretly Share Private Information With US Chip-Maker https://www.nitrokey.com/news/2023/smartphones-popular-qualcomm-chip-secretly-share-private-information-us-chip-maker
(Apologies to Rick Astley)
We're no strangers to hacks
You know the column, and so do I
A full published book's what I'm thinking of
You wouldn't get this from any other guy
I just wanna tell you what I've written
Gotta make you understand
It's the Best of Hack and /
It's a Linux admin class
You can order and real fast send to you
Hardback's awesome I won't lie
Paperback is a close tie
With the ebook you can buy on Lulu
@cavaughan I have a Comptometer manual that goes into how to do more advanced things like roots, but it seemed complicated enough that I'd never know if I got the right answer.
@cavaughan Once you know addition and subtraction, then multiplication is just repeated addition, with shifts to the left for each digit in the multiplier. Division is similar, but starts at the left of the dividend, and you subtract repeatedly until it underflows (the machine will ring a bell!) and then you add one back and shift right. Repeat until you have enough digits of precision to suit you.
@cavaughan I have a pinwheel calculator just like that! But not a Russian model, it is a Brunswiga.
- Personal Site
- https://kylerank.in
- Personal Bibliography
- https://kylerank.in/writing.html
Technical author, FOSS advocate, public speaker, Linux security & infrastructure geek, author of The Best of Hack and /: Linux Admin Crash Course, Linux Hardening in Hostile Networks and many other books, ex-Linux Journal columnist.
