I was interviewed about supply chain security (around 15 min mark) in a longer CNBC feature about manufacturing phones in the USA. In short, it's less about trust concerns with any particular country/govt., and more about reducing the links in the supply chain to reduce the opportunities to tamper with hardware.
Our Made-in-USA-electronics Librem 5 USA phone also got a number of shout-outs. Pretty neat!
https://youtu.be/YdbA7Z8Ae4w #security #supplychain #infosec #manufacturing
I'm not that enthusiastic about Google, Apple and Microsoft doing away with #passwords as an #authentication factor, because it's one of the few areas left on these platforms where people have some control over their own #security. #infosec https://puri.sm/posts/microsoft-ruined-passwords-now-aims-for-a-passwordless-future/
I realized I hardly ever add topical hashtags to posts which probably makes it tougher for folks around the fediverse to see things I write that they might be interested in. I'll try to do better with future posts about #weaving , #calculators , #addingmachines and #Linux #FOSS and #infosec topics.
I wrote about our unique set of high security features for the Librem 14 such as anti-interdiction, Qubes, hardware kill switches, and PureBoot. What other security features would you like to see us add to this in the future? #infosec #hardening https://puri.sm/posts/my-recommendations-for-the-most-secure-librem-14-configuration/
Check out this Dice article by @yaelwrites on how to build a career in #infosec. Bonus: I'm quoted in it! https://insights.dice.com/2020/08/04/cybersecurity-expert-careers-skills-embrace-pitfalls-avoid/
One of the most damaging philosophies #infosec copied from IT is a belief in user inferiority. Too many security decisions are rooted in a patronizing notion that users are children and that trust and agency must be taken from them and given to infosec staff/vendors.
Surveillance vendor NSO Group pitched hacking tools to US police forces that would "turn your target's smartphone into an intelligence gold mine" #privacy #infosec https://www.vice.com/en_us/article/8899nz/nso-group-pitched-phone-hacking-tech-american-police
Attacks like this are likely not limited to Zoom (it just has #infosec attention now). If your computer has a hardware kill switch (HKS), disable camera+mic except during video conferences. If you don't have a HKS, cover the camera in between uses: https://9to5mac.com/2020/04/01/new-zoom-bugs-takeover-macs-cam-mic-root/
If you are going to #SCALE18x this weekend check out my talk on Saturday at 15:00 titled "Heads: Tamper-evident Firmware with User-controlled Keys" #infosec https://www.socallinuxexpo.org/scale/18x/presentations/heads-tamper-evident-firmware-user-controlled-keys
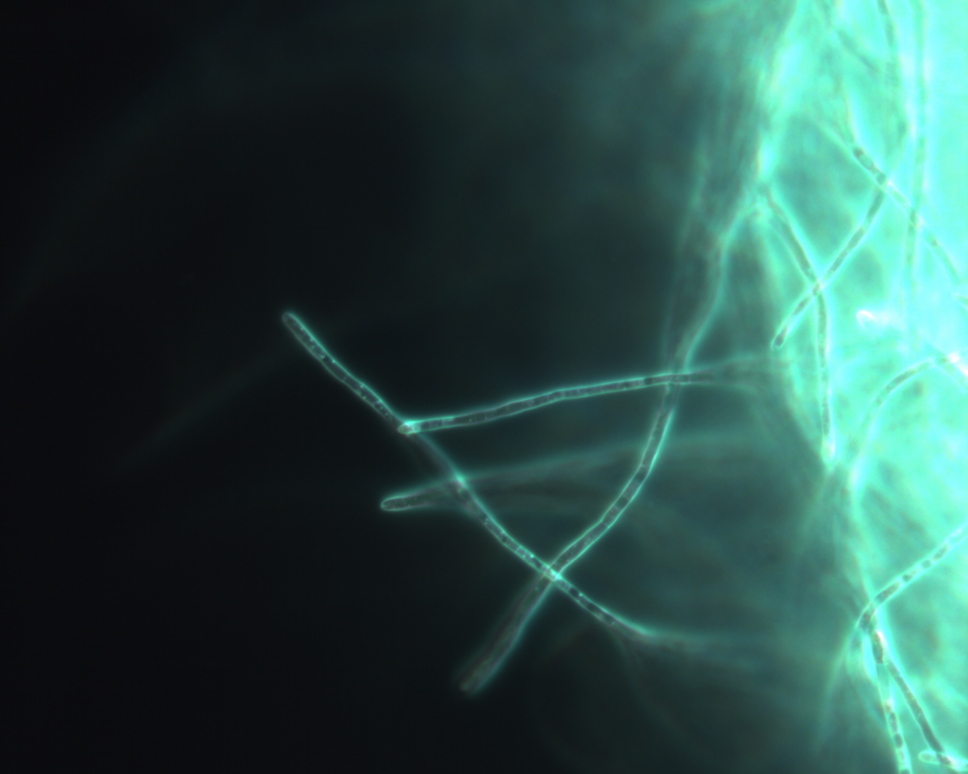
I've really enjoyed processing our new-and-improved anti-interdiction orders. So far I have to say out of all the glitter nail polish, orange is my favorite (looks so cool against the black case) followed by rainbow. #infosec #tamperevident
A reminder that biometric auth security is not based on secrecy (#biometrics aren't secret), but on the difficulty of making a copy that can trick a sensor. Now there's an app for that. #infosec
https://fossbytes.com/a-new-app-can-scan-fingerprints-from-drinking-glass-to-unlock-your-device/
I've said it before and I'll say it again: the most persistent, resourceful and difficult adversaries to secure against are kids behind parental/school controls and employees behind corporate firewalls: #infosec https://www.washingtonpost.com/technology/2019/10/15/teens-find-circumventing-apples-parental-controls-is-childs-play/
"The researchers have named their attack NetCAT, short for Network Cache ATtack"
Seriously, netcat? I guess what they say about the two hardest problems in computer science is true... #infosec https://arstechnica.com/information-technology/2019/09/weakness-in-intel-chips-lets-researchers-steal-encrypted-ssh-keystrokes/
After decades of suffering through ipchains/iptables syntax, and seeing how easy fw and ufw made common firewall workflows, it's disappointing that the best Debian's iptables replacement can do is:
nft add rule inet filter input tcp dport 22 accept
When syntax for common workflows is complicated, you increase the chance the admin will make a mistake that exposes them to attackers. See S3 bucket permissions for more examples of this. #infosec #devops
It's not too late for bug bounty companies to source practical grasshopper-plague-related swag. Swatters, bug spray, mesh netting: #infosec #plagueoflocusts #defcon #blackhat https://www.nytimes.com/2019/07/27/us/grasshoppers-vegas.html
I ran into a new security measure the other day: my bank has added complexity requirements to *usernames* now, presumably to make them harder to guess and brute force attacks more difficult. #infosec
Whoever named this needs a lesson in modern #infosec malware branding. "eCh0raix" really? NASty NAP is the obvious choice: https://www.zdnet.com/article/this-new-ransomware-is-targeting-network-attached-storage-devices/
I imagine many in #infosec will conclude the ends justify the means, and I imagine most Apple users won't care, but I still think silently pushing non-interactive 3rd-party app updates to consumer devices is creepy: https://techcrunch.com/2019/07/10/apple-silent-update-zoom-app/
- Personal Site
- https://kylerank.in
- Personal Bibliography
- https://kylerank.in/writing.html
Technical author, FOSS advocate, public speaker, Linux security & infrastructure geek, author of The Best of Hack and /: Linux Admin Crash Course, Linux Hardening in Hostile Networks and many other books, ex-Linux Journal columnist.
